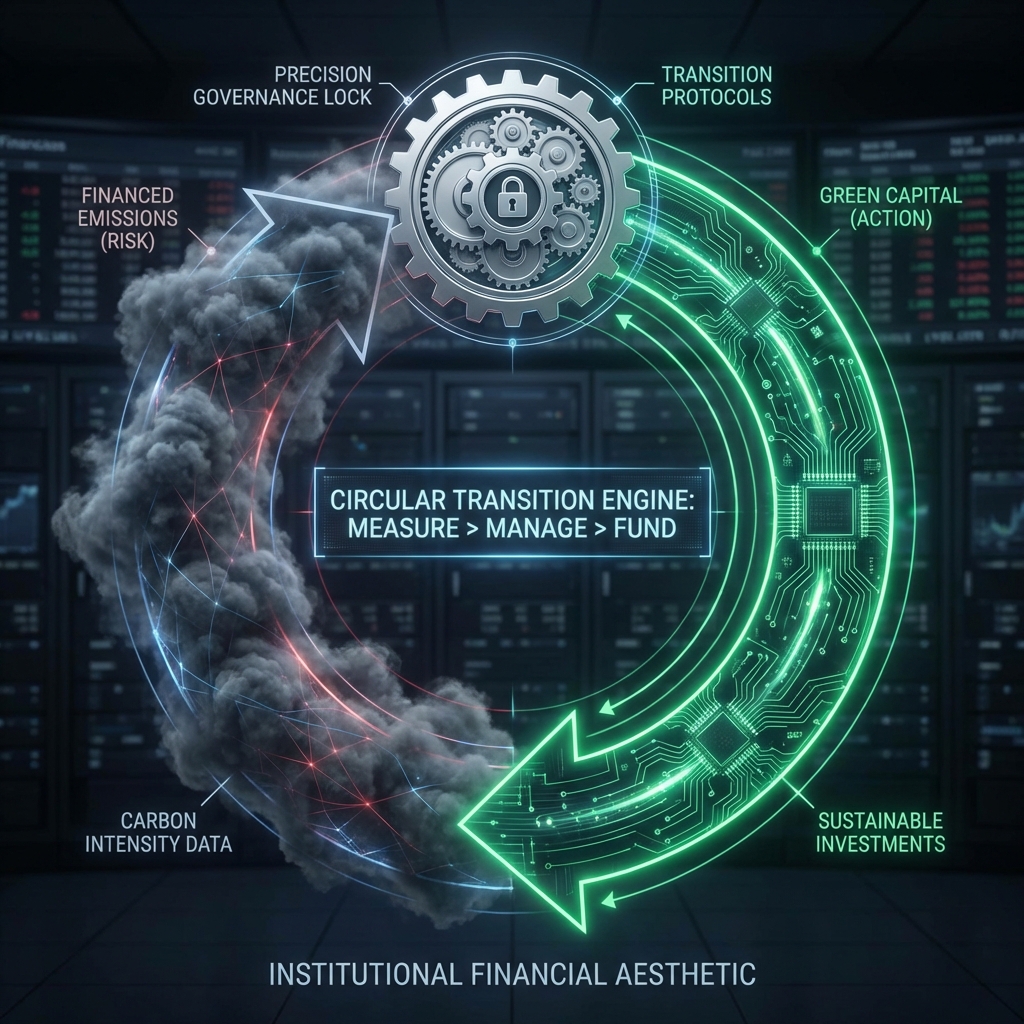
Hidden Discretion
Manual overrides and unversioned spreadsheets aren't just messy - they are functionally unverifiable. Accountability diffuses into "the team," rendering the audit void.
Single-Person Accountability
Every workspace enforces one named approver. No admin override. No silent bypass. Every decision is cryptographically signed.